This developer diary will cover the plugin User Profile Picture, a WordPress plugin.
This past week has been somewhat unproductive. I keep suffering from anxiety and panic attacks, which affects my work. Luckily my doctor knows what he’s doing and put me on a new cocktail to help combat the anxiety attacks. Time will tell as always if it’ll work in the long-term.
Let’s move onto the topic of WordPress plugin security.
User Profile Picture
It was brought to my attention there was a medium-level security issue with User Profile Picture. When I first heard about it, I was put into guessing mode… “What was the problem, how hard is it to fix, and what are the consequences?”
Chloe Chamberland from Wordfence was kind enough to point out a security issue with one of my old plugins. Wordfence, in short, is awesome for this service they provide for the WordPress community.
Since I’ve sold User Profile Picture to Cozmoslabs, they received the security tip. Since I’m most familiar with the code-base, Cozmoslabs reached out to me to perform a hot security fix to the plugin.
The Security Flaw
I’ll wait until Wordfence publishes their disclosure post, but the crux of the issue is the potential for a user with the upload_files permission to be able to see user data if they were to have malicious intent. Since the upload_files permission can be given to the Contributor, Subscriber, and/or other roles, it was important that we fix the security issue for the users as soon as possible.
I’ll update this section once Wordfence publishes their post.
The Recommendations
After the security flaw was patched and fixed, I asked for best practices for disclosing from Wordfence’s perspective. It was recommended to:
- Disclose as much as possible so users can know to upgrade based on a security flaw.
- Help spread the word about the vulnerability without giving “too” much away.
- New point release to more easily track users who are on the “fixed” version.
- A post describing the issue (does this one count?).
Damned If You Do
We fixed the security flaw and gave users a stark warning in the changelog:
Medium level (6.5) security fix. Please update as soon as possible.
Cleaned up REST user data so only pertitent [sic] information is returned to prevent user data leakage to roles with the upload_files capability.
Ronald Huereca
I expected a wave of updates of the plugin, but unfortunately we lost users. The plugin recently reached the 60,000+ installs milestone, and it sharply dipped after the update.
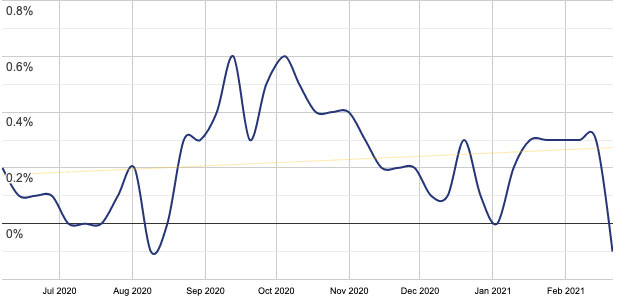
Things have stabilized for now, but I’m hoping the kinks can work out, users upgrade, and we can all win together with a more secure plugin.
Damned If You Don’t
Obviously, the ramifications of leaving an insecure plugin in the Plugin Directory is very problematic. Plugins with active and exploitable security flaws are a big issue, and the WordPress plugin team would rightfully remove the plugin should the security flaw not be fixed.
As a result, after the fix, I emailed the WordPress plugin and security teams to let them know about the problem and our fix. They thanked us for being proactive about disclosing.
A Path Forward
It’s never a good day when you discover a security flaw with the potential to impact so many users. We’ve done our best, and hope that people will continue using the plugin.
This isn’t the first time one of my plugins has had a security flaw, and I’m sure it will not be the last, but I feel like I did my best to mitigate the issue after discovering it.